Archaic Rhymes.
Apr. 8th, 2026 10:03 pmAnatoly Vorobey has a Facebook post that starts with a reference to a video in which Oleg Lekmanov compares a bunch of clips of people reading aloud the first stanza of Pushkin’s “Анчар” (The Upas Tree; there are a number of English translations, e.g. A.Z. Foreman, Michael Allen) to see if they read the last word in the second line as “раскалённой” (raskalyonnoi, the normal reading in modern Russian) or “раскаленной” (raskalennoi, with e as in Church Slavic, to rhyme with the final word of the stanza, “вселенной” [vselennoi] ‘universe’). Anatoly says it seems to him this is a sort of intelligentsia shibboleth, with a snobbish preference for the Church Slavic as “correct” (he quotes a textbook to that effect), whereas he thinks both pronunciations have a right to exist — a conclusion with which I, naturally, concur. One of his commenters brings up English rhymes like rove/love, but this seems to me a different, though parallel, case.
In any case, the Pushkin quote led me to look up the word анчар (apparently first used in this poem), which according to Russian Wiktionary (citing Vasmer) is borrowed from Dutch antjar, itself from Malay ančar. Amazingly (to me), the OED has an entry (from 1885) for antiar ‘The Upas tree of Java, Antiaris toxicaria; also, the poison obtained from it’; there are no citations, but there is an etymology: “< Javanese antjar, antschar.” And upas itself (entry from 1926) is “< Malay ūpas poison, in the combination pōhun (or pūhun) ūpas poison-tree.” All roads lead to Malaya.
Meadow writing
Apr. 8th, 2026 09:37 pmFrom "Everyday Politics in Russia", The Eurasian Knot 4/6/2026:
The podcast starts with a message from listener Amanda, who has been reading all of Dostoevsky for a workshop in Russia. In addressing the podcast's host Sean Guillory, she says (starting at 4:21.5):
I sympathize with you, Sean, that you just couldn't get into him,
but I've personally never felt that way about Dostoevsky.
I remember trying to read the Lord of the Rings series,
and I couldn't stand it.
I couldn't stand ten pages describing a meadow.
And ever since them I've thought of fiction writing in terms of
meadow-writing and non-meadow-writing.
No wonder I love Dostoevsky —
he has nothing whatsoever to say about meadows.
"Meadow-writing" is a strikingly evocative name for a stylistic category, but I'm puzzled about its concrete reference. The Fellowship of the Ring has six occurrences of the word "meadow", scattered in the background of six (mostly non-consecutive) pages. The Two Towers has two occurrences of that word. The Return of the King has just one.
Update — PGilm in the comments combines a good general point — "that Amanda wasn't complaining about meadows specifically but about landscape description generally" as kschwatz puts it — with quotations that are entirely hallucinated, as kschwartz also notes. I found that PGilm had commented once before in 2019 as "Philip", with the same email address, in both cases from a Verizon IP address in Scarsdale, suggesting that he's a real person even if his comment on this post was partly or entirely bot-generated.
(no subject)
Apr. 8th, 2026 05:10 pmFinished nothing but a Dr Priestley or two this week. Tiktok is all I'm up for in these antsy latter days.
Banning New Foreign Routers Mistargets Products to Fix Real Problem
Apr. 8th, 2026 07:24 pmOn March 23, the FCC issued an update to their Covered List, a list of equipment banned from obtaining regulatory approval necessary for U.S. sale (and thus effectively a ban on sale of new devices), to include all new routers produced in foreign countries unless they are specifically given an exception by the Department of Defense (DoD) or DHS. The Commission cited “security gaps in foreign-made routers” leading to widespread cyberattacks as justification for the ban, mentioning the high-profile attacks by Chinese advanced persistent threat actors Volt, Flax, and Salt Typhoon. Although the stated intention is to stem the very real threat of domestic residential routers being commandeered to initiate attacks and act as residential proxies, this sweeping move serves as a blunt instrument that will impact many harmless products. In addition to being far too broad, it won’t even affect many vulnerable devices that are most active in these types of attacks: IoT and connected smart home devices.
Previously, the FCC had changed the Covered List to ban hardware by specific vendors, such as telecom equipment produced by companies Huawei and Hytera in 2021. This new blanket ban, in contrast, affects the importation and sale of almost all new consumer routers. It does not affect consumer routers produced in the United States, like Starlink in Texas. While some of the affected routers will be vulnerable to compromises that hijack the devices and use them for cybercrime and attacks, this ban does not distinguish between companies with a track-record of producing vulnerable products and those without. As a result, instead of incentivizing security-minded production, this will only limit the options consumers have to US-based manufacturers not affected by the ban—even those that lack stellar security reputations themselves.
While the sale of vulnerable routers in the U.S. will not stop, the announcement quoted an Executive Branch determination that foreign produced routers introduce “a supply chain vulnerability that could disrupt the U.S. economy, critical infrastructure, and national defense.” Yet this move does nothing to address the growing number of connected devices involved in the attacks this ban aims to address. As we have previously pointed out, supply chain attacks have resulted in no-name Android TV boxes preloaded with malware, sold by retail giants like Amazon, fuelling the massive Kimwolf and BADBOX 2 fraud and residential proxy botnets. Banning the specific models and manufacturers we know produce dangerous devices putting its purchasers at risk, rather than issuing blanket bans punishing reputable brands that do better, should be the priority.
With the FCCs top commissioner appointed by the President, this ban comes as other parts of the administration impose tariffs and issue dozens of trade-related executive orders aimed at foreign goods. A few larger companies with pockets deep enough to invest in manufacturing plants within the U.S. may see this as an opportune moment, while others not as well poised to begin U.S. operations may attempt to curry enough favor to be added to the DoD or DHS exception lists. At best, this will result in the immediate effect of an ill-targeted policy that does little to improve domestic cybersecurity posture. At worst, it entrenches existing players and deepens problematic quid-pro-quo arrangements.
American consumers deserve better. They deserve the assurance that the devices they use, whether routers or other connected smart home devices, are built to withstand attacks that put themselves and others at risk, no matter where they are manufactured. For this, a nuanced, careful consideration of products (such as was part of the FCC’s 2023-proposed U.S. Cyber Trust Mark) is necessary, rather than blanket bans.
Vitiation of argumentation by AI participation
Apr. 8th, 2026 07:06 pmThe battlelines are being drawn ever clearer. On one side are those who believe that it's all right to use AI to help with the preparation of an (academic) article, essay, or paper. On the other side are those who think that the utilization of AI is impermissible for such purposes. As soon as they discern the use of AI in writing a composition, they will dismiss it out of hand. Use of AI extends to the collection and organization of material to be included in what is being written.
Readers who are sensitive to the stylistics of AI writing can even detect it in punctuation preferences, rhetorical tone, lexical propensities, and so forth.
There are even commercially available "AI detectors", e.g.: "Pangram can detect AI-generated text even after it has been 'humanized,' or processed by tools that attempt to evade AI detection, ensuring reliable detection."
This confrontation between pro-AI and anti-AI praxis will continue apace until some sort of stasis / equilibrium is attained or one side overwhelms / cannibalizes the other.
Afterword
I know many people who have made AI (e.g., ChatGPT) their personal friend and constant companion.
Bottom line
The human signs off at the end.
Selected readings
- "Writing with AI" (9/1/24)
- "AI triumphs… and also fails." (10/3/24)
- and countless other Language Log posts
Another Court Rules Copyright Can’t Stop People From Reading and Speaking the Law
Apr. 8th, 2026 06:13 pmAnother court has ruled that copyright can’t be used to keep our laws behind a paywall. The U.S. Court of Appeals for the Third Circuit upheld a lower court’s ruling that it is fair use to copy and disseminate building codes that have been incorporated into federal and state law, even though those codes are developed by private parties who claim copyright in them. The court followed the suggestions EFF and others presented in an amicus brief, and joined a growing list of courts that have placed public access to the law over private copyright holders’ desire for control.
UpCodes created a database of building codes—like the National Electrical Code—that includes codes incorporated by reference into law. ASTM, a private organization that coordinated the development of some of those codes, insists that it retains copyright in them even after they have been adopted into law, and therefore has the right to control how the public accesses and shares them. Fortunately, neither the Constitution nor the Copyright Act support that theory. Faced with similar claims, some courts, including the Fifth Circuit Court of Appeals, have held that the codes lose copyright protection when they are incorporated into law. Others, like the D.C. Circuit Court of Appeals in a case EFF defended on behalf of Public.Resource.Org, have held that, whether or not the legal status of the standards changes once they are incorporated into law, making them fully accessible and usable online is a lawful fair use.
In this case, the Third Circuit found that UpCodes’s copying of the codes was a fair use, in a decision closely following the D.C. Circuit’s reasoning. Fair use turns on four factors listed in the Copyright Act, and the court found that all four favored UpCodes to some degree.
On the first factor, the purpose and character of the use, the court found that UpCodes’s use was “transformative” because it had a separate and distinct purpose from ASTM—informing people about the law, rather than just best practices in the building industry. No matter that UpCodes was copying and disseminating entire safety codes verbatim—using the codes for a different purpose was enough. And UpCodes being a commercial venture didn’t change the outcome either, because UpCodes wasn’t charging for access to the codes.
On the second factor, the nature of the copyrighted work, the Third Circuit joined other appeals courts in finding that laws are facts, and stand at “the periphery of copyright’s core protection.” And this included codes that were “indirectly” incorporated—meaning that they were incorporated into other codes that were themselves incorporated into law.
The third factor looks at the amount and substantiality of the material used. The court said that UpCodes could not have accomplished its purpose—providing access to the current binding laws governing building construction—without copying entire codes, so the copying was justified. Importantly, the court noted that UpCodes was justified in copying optional parts of the codes as well as “mandatory” sections because both help people understand what the law is.
Finally, the fourth factor looks at potential harm to the market for the original work, balanced against the public interest in allowing the challenged use. The court rejected an argument frequently raised by copyright holders—that harm can be assumed any time materials are posted to the internet for all to access. Instead, the court held that when a use is transformative, a rightsholder has to bring evidence of harm, and that harm will be balanced against the public benefit. Because “enhanced public access to the law is a clear and significant public benefit,” and ASTM hadn’t shown significant evidence that UpCodes had meaningfully reduced ASTM’s revenues, the fourth factor was at least neutral. It didn’t matter to the court that ASTM offered to provide copies of legally binding standards to the public on request, because “the mere possibility of obtaining a free technical standard does not nullify the public benefits associated with enhanced access to law.”
This is a good result that will expand the public’s access to the laws that bind us—something that’s more important than ever given recent assaults on the rule of law. In the future, we hope that courts will recognize that codes and standards lose copyright when they are incorporated into law, so that people don’t have to spend years and legal fees litigating fair use just to exercise their rights.
👁 Selling Mass Surveillance | EFFector 38.7
Apr. 8th, 2026 04:24 pmTime and time again, we've seen police surveillance suffer from 'mission creep'—technology sold as a way to prevent heinous crimes ends up enforcing traffic violations, tracking protestors, and more. In our latest EFFector newsletter, we're diving into this troubling pattern and sharing all the latest in the fight for privacy and free speech online.
For over 35 years, EFFector has been your guide to understanding the intersection of technology, civil liberties, and the law. This week's issue covers the urgent need to reform NSA spying; a victory for internet access in the Supreme Court; and how license plate readers are normalizing mass surveillance.
Prefer to listen in? EFFector is now available on all major podcast platforms. This time, we're chatting with EFF Privacy Litigation Director Adam Schwartz about some of the recent technologies we've seen suffer from "mission creep." And don't miss the EFFector news quiz! You can find the episode and subscribe on your podcast platform of choice:

Want to help us push back against mass surveillance? Sign up for EFF's EFFector newsletter for updates, ways to take action, and new merch drops. You can also fuel the fight for privacy and free speech online when you support EFF today!
HHS issues new guidelines for food served in hospitals
Apr. 8th, 2026 01:00 pmMehmet Oz’s Centers for Medicare & Medicaid Services (CMS) sent a memo to hospitals last week, telling them to align their food service policies and practices with the 2025–2030 dietary guidelines (see announcement in video).
Hospitals should:
• Limit ultra-processed food options for patients.
• Eliminate sugar-sweetened beverages unless clinically appropriate in limited scenarios.
• Eliminate refined grains and replace them with 100% whole grains.
• Prioritize minimally processed protein sources, including plant-based options.
• Emphasize vegetables, fruits, legumes, nuts, seeds, seafood, and healthy fats.
• Ensure baked, broiled, roasted, stir-fried, or grilled vegetables and proteins – and eliminate deep fried cooking methods
• Eliminate processed meats and foods high in added sugars, sodium, and artificial additives.
• Ensure meals contain less than 10 grams of added sugar, unless clinically appropriate.
These sound terrific!
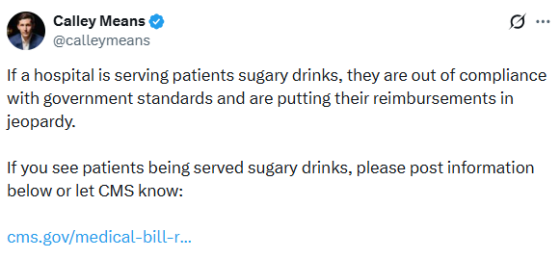
According to RFK Jr’s advisor, Calley Means, these guidelines will be enforced.
Hospital food, of course, has been criticized heavily for decades. A hospital director once explained to me that it was the only place in his budget that was discretionary, the only option he had for cutting spending, which he did.
But as always, the situation is complicated and the devil is in the details. Kevin Klatt, a nutrition professor in Toronto, questions on his Substack whether this is “anything more than the nutrition political theatre that we’ve come to expect from this federal administration/MAHA?”
He reviews the regulatory issues but also points out that clinical (hospital-based) nutrition is not the same as public health nutrition.
Patients who are acutely ill and hospitalized are not the general public that the DGAs are made for…Patients who are hospitalized often have conditions that impact their nutritional requirements, alter their ability to digest, absorb, and assimilate nutrients, and major barriers to consuming a normal diet – everything from altered taste and smell to the inability to chew and swallow…It’s clear no clinical dietitians…were in the room when this memo was put out…or it was always meant as more political performance before the midterms, as RJK Jr is being encouraged to quiet down on vaccines and play to his foodie base.
Yes, clinical dietitians must deal with their patients’ needs.
But surely these rules ought to apply to the hospital cafeterias and vending machines that serve visitors and staff. That alone would be a big step forward.
Here too, I can’t wait to see how it all plays out.
The post HHS issues new guidelines for food served in hospitals appeared first on Food Politics by Marion Nestle
Witch Hat Atelier, volume 14 by Kamome Shirahama
Apr. 8th, 2026 08:53 am
Coco and chums have an innovative cure for the monster currently rampaging through town... an innovative cure from which a diligent cop is determined to protect society.
Witch Hat Atelier, volume 14 by Kamome Shirahama
Where leaves are emerging and flowers are blooming
Apr. 8th, 2026 10:10 amIt’s that time of year again when we hear about how the plants are growing across the country. For the Washington Post, Ben Noll, John Muyskens, and Naema Ahmed have the maps for leaves and flowers.
Meteorological spring started March 1. The astronomical season started March 20. But there’s a third option: The season as decreed by the plants. They don’t follow any calendar and instead leaf out when it’s warm enough.
The first emergence of leaves can be estimated by temperatures since the start of the year. A certain amount of warmth needs to accumulate before leaves appear. This warmth is typically measured through a metric called growing degree days.
Tags: growth, spring, Washington Post
Digital Hopes, Real Power: How the Arab Spring Fueled a Global Surveillance Boom
Apr. 8th, 2026 08:22 amThis is the third installment of a blog series reflecting on the global digital legacy of the 2011 Arab uprisings. You can read the first post here, and the second here.
When people recall the 2011 uprisings across the Middle East and North Africa (MENA), they often picture crowded squares, raised phones, and the feeling that the internet had finally shifted the balance of power toward ordinary people. But the past decade and a half is also a story about how governments, companies, and platforms turned those same tools into the backbone of a powerful state surveillance apparatus.
For activists, journalists, everyday users, that means now living with a constant threat. The phone in your pocket, the platforms you organize on, and the systems you rely on for safety and connection can be weaponized at the flip of a switch. A global surveillance industry has treated repression by many MENA governments as a growth opportunity, and the tactics refined there now shape digital authoritarianism worldwide. This essay traces how that shift unfolded: security agencies upgraded older systems of repression with new surveillance tools and permanent monitoring infrastructure; cybercrime laws and mercenary spyware markets turned digital control into standard operating procedure; and biometrics, facial recognition, and ‘smart city’ projects laid the groundwork for AI‑driven surveillance that now shapes protests, borders, and everyday life far beyond the region.
Remembering the Arab Spring means seeing the events of 2011 as both a remarkable moment of movement history when people leveraged networked tools in their fight for freedom and the beginning of a long, grinding effort to turn those same tools into mechanisms of state control.
Old‑School Repression, New‑School Tools
Long before Facebook and Twitter, regimes in countries like Egypt and Syria already knew how to crush dissent. They leaned on informant networks, physical surveillance, and wiretaps, backed by emergency laws that let security agencies monitor and detain critics with almost no restraint. Research on the use of surveillance technology in MENA shows that, even before the Arab Spring, states were layering early digital tools like internet monitoring, deep packet inspection, and interception centers on top of that older machinery of control.
At the same time, connectivity was racing ahead. Cheap smartphones and social media suddenly let people share information at scale, coordinate protests, and broadcast abuses in real time. In 2011, EFF described both the excitement around “Facebook revolutions” and the early signs that governments were scrambling to upgrade their capacity to watch and disorganize popular dissent.
After the uprisings, Western critics endlessly debated how much credit to give social media itself. While in the background, security agencies across several MENA states reached a much simpler conclusion: if networked communication can help topple a dictator, then they needed to embed themselves deep inside those networks. Analyses of the rise of digital authoritarianism in MENA show how quickly officials pivoted from being surprised by online organizing to building systems to monitor and pre‑empt it.
In the years after 2011, governments across the region poured money into tools that let them systematically watch what people said and did on major platforms. Foreign vendors set up monitoring centers and interception systems that let security agencies block tens of thousands of sites, scrape and analyze social media at scale, monitor activist pages and online communities, and track activists in real time. They built a new, pre‑emptive model of digital control, one that assumes the state should see as much as possible, as early as possible.
As we noted in 2011, exporting permanent surveillance infrastructure to already‑abusive governments doesn’t “modernize” public safety; it locks in an architecture of control that is primed to abuse dissidents, journalists, and marginalized communities.
Domestic Lawfare and Cyber-Mercenaries
After the uprisings, a number of governments also rewrote the rules that govern online life. Cybercrime laws, “fake news” provisions, and overbroad public‑order and ‘morality’ offences gave prosecutors and security agencies legal cover to act with impunity. Governments in Saudi Arabia, Tunisia, Jordan, and Egypt combined counterterrorism, cybercrime, defamation, and protest laws into a legal thicket designed to make online dissent feel dangerous and costly. Morality laws and cybercrime provisions are used to target queer and trans people based on identity and expression.
At the United Nations, a new global cybercrime convention now risks baking this logic into international law. The convention was adopted by the UN General Assembly in late 2024, despite serious human rights concerns raised by civil society. Echoing our partners, EFF warned at the time that the UN cybercrime draft convention remained too flawed to adopt and urged states to reject the draft language because it legitimized expansive surveillance powers and criminalized legitimate expression, security research, and everyday digital practices around the world. While on paper, these instruments gesture to “public safety” objectives, in practice they function as pathways for state security agencies to monitor, prosecute, and silence the communities most at risk. For state-targeted communities, that makes being visible online a calculated risk, not a neutral choice.
Criminal codes are only half the story; mercenary tech is the other. As governments worldwide looked for ways to outpace their critics, a parallel market emerged to help them infiltrate and take over devices. Companies like NSO Group marketed Pegasus and similar tools as off‑the‑shelf capabilities for governments that wanted to hack a target’s cellphones or other devices to read messages, turn on microphones, and monitor entire social networks while bypassing the courts.
In 2019, UN Special Rapporteur David Kaye called for a global moratorium on the sale and transfer of private surveillance tools until real, enforceable safeguards exist. Two years later, forensic work by Amnesty and media partners showed how the same spyware used to hack phones of Palestinian human‑rights defenders was used to surveil journalists, activists, lawyers, and political opponents across dozens of countries.
Regional groups responded by demanding an end to the sale of surveillance technology to autocratic governments and security agencies, arguing that you cannot keep selling “lawful intercept” tools into systems where law itself is an instrument of repression. Commercial spyware is at the center of digital repression, not at its margins. Surveillance vendors are not neutral suppliers. Safeguards remain weak, fragmented, or nonexistent in most of the countries buying these tools, yet vendors continue seeking new contracts and new militarized “use cases.” Put bluntly, the companies that design, market, and maintain these systems precisely because they enable this kind of control profit from (and help entrench) authoritarian power.
Biometrics, Facial Recognition, and AI‑Powered Surveillance Cities
On top of this rapidly intensifying interception and spyware stack, governments and companies began layering biometrics and face recognition into everyday systems, creating pathways for bulk data collection, automated analysis, and risk profiling. In parts of MENA, national ID schemes, border and migration controls, and centralized biometric databases have been rolled out in environments with weak or captured data‑protection laws, making it easy to link people’s movements, services, and political activity to a single, persistent identifier.
Humanitarian programs are not exempt from this protocol. In Jordan, Syrian refugees have been required to submit iris scans and biometric data to access cash assistance and food, turning “consent” into a precondition for survival. When access to aid depends on enrollment in centralized biometric systems, any breach, misuse, or repurposing of that data can have severe, life‑altering consequences for people who have no realistic way to opt out. Investigations into surveillance‑tech firms complicit in abuses in MENA show that vendors profit from supplying biometric and surveillance tools for migration management and internal security, even when those tools are used in discriminatory or abusive ways.
Like elsewhere, mass surveillance technologies in MENA were first piloted on people who were already criminalized or made vulnerable by poverty. But their use quickly expanded from narrow, security‑framed deployments to routine use in city streets. As hardware sensors, cameras, and data storage got cheaper, “smart city” surveillance systems promised seamless security and services, and it became easier and less politically contentious to keep these systems running everywhere, all the time.
Unlike targeted hacking tools, these broad, city‑wide surveillance infrastructures erase any practical line between people under investigation and the broad public, normalizing bulk, indiscriminate monitoring of public space and everyday movement. In the Gulf, facial recognition and dense sensor networks are increasingly built into high‑profile “smart city” and mega‑project plans that lean heavily on biometric and AI‑driven monitoring. These are security‑first development projects where biometric and sensor infrastructures are designed from the outset to embed policing, migration control, and commercial tracking into the urban fabric. In this vision of the Gulf’s “smart city” future—often sold as seamless services and digital opportunity—“smart” is the branding, and pervasive monitoring is the operating principle.
EFF has consistently opposed government use of face recognition and biometric surveillance, in some instances calling for outright bans. In contexts that treat peaceful dissent as a security threat, embedding biometric surveillance into everyday infrastructure locks in a balance of power that favors militarized policing and state control. That infrastructure is now the starting point for a new set of risks. Surveillance systems built over the last decade are being repackaged as the foundation for a new generation of “AI‑enabled” defense and security products.
Companies that once focused on video management or perimeter security now advertise “defense applications” for AI‑driven situational awareness and threat detection, using computer‑vision models to scan camera feeds, compare against existing watchlists, and flag “suspicious” people or behaviors in real time. Drone and sensor platforms are being upgraded with embedded AI that tracks and classifies targets autonomously and with “drone‑based AI threat detection and intelligent situational awareness,” turning aerial surveillance into a continuous data feed for security agencies and militaries. In smart‑city and defense expos from the Gulf to Europe and North America, similar systems are marketed as neutral efficiency upgrades or tools to “protect critical infrastructure,” even where they are explicitly designed to scale up border enforcement, protest surveillance, and internal security operations.
As these systems are folded into AI‑driven defense products, the line between “civilian” infrastructure and militarized surveillance disappears, turning streets, borders, and aid sites into continuous input for security operations. That is the landscape that human rights and accountability efforts now have to confront.
Templates of Control, Networks of Resistance
The patterns established in heavily securitized MENA states after the Arab Spring now shape how states monitor and crush more recent uprisings, from Iran’s use of location data and facial recognition to track down protesters to long‑running crackdowns elsewhere in the region. This model of “digital authoritarianism” built on spyware, data‑hungry ID systems, platform control, and emergency‑style security laws has emerged everywhere from Latin America to Eastern Europe to here in the United States. As the new UN Cybercrime Convention moves toward implementation, its broad offences and surveillance powers risk turning this ad hoc toolkit into a formal template for cross‑border data‑sharing, repression, and an all‑purpose global surveillance instrument.
For people on the ground, none of this is theoretical. Human‑rights defenders, journalists, and ordinary users across the region face arrest, long prison sentences, and exile based on their digital traces. In that context, commercial spyware is not a marginal issue but part of the core machinery of repression. Pegasus has been used to hack journalists’ phones through zero‑click exploits and compromise human‑rights defenders and watchdog organizations themselves, including staff at Amnesty’s Pegasus Project partners and Human Rights Watch. These deployments give practical effect to the “cybercrime” and “terrorism” frameworks described earlier: person‑by‑person campaigns against particular communities, contacts, and networks, rather than “neutral,” generalized security measures.
Under these conditions, everyday security becomes a second job. People describe carrying multiple phones, keeping one for relatively “clean” uses and others for riskier conversations, splitting identities across platforms, using coded language, and moving their organizing off mainstream services when possible. Pushing this burden onto users is a political choice: states, platforms, and vendors could build systems that are safe by design; instead, they externalize risk to the people they watch and punish.
Even against that backdrop, civil society organizations have refused to capitulate to security agencies and vendors. Regional coalitions have demanded strict export controls and outright bans on selling intrusive surveillance tech to autocratic governments. Advocates have also pushed companies to do more than box‑ticking “due diligence.” Work with surveillance‑tech firms in the context of migration and border control has repeatedly shown that most are still far from serious human‑rights assessments, let alone willing to turn down these lucrative contracts.
Many of the same governments that have been critical of others on the issue of human rights have hosted or licensed companies that build these tools, in some cases buying similar capabilities for their own security agencies. European authorities, for instance, have investigated FinFisher’s export of spyware “made in Germany” to Turkey and other non‑EU governments. Meanwhile, the NSO Group has at least 22 Pegasus contracts with security and law‑enforcement agencies in 12 EU countries. This is a transnational industry, not a localized problem.
Against near impossible odds, people continue finding pathways to freedom. The global surveillance sector reinforces the same hierarchies and violence that people have found ways to survive for generations. Queer activists and others at the sharpest edges of this system have had to develop their own forms of resistance, including against biometric and data‑driven targeting. Encryption, circumvention tools, and security training are not silver bullets, but they remain essential for anyone trying to organize, document abuses, or simply exist online with a bit less risk. Resources like EFF’s Surveillance Self‑Defense are one piece of that ecosystem, alongside trainers and groups who have been doing this work on the ground for years.
Defending the Future of Digital Dissent
The Arab Spring is often remembered through images of packed squares and hopeful tweets. But contending with its aftermath means confronting the surveillance architecture built in its shadow: laws that turn online speech into a crime, spyware and biometric systems that turn phones and faces into tracking beacons, and platform practices that routinely sacrifice the people most at risk. None of that is inevitable, and none of it is confined to one part of the world.
Accountability has to reach both governments and the companies that profit from arming them with these tools. That means pushing for far stronger limits on how surveillance tech is built, sold, and deployed; demanding meaningful transparency when these systems are used; and defending the tools people rely on to communicate and organize safely, including robust encryption and secure channels. It also means taking direction from the people and communities who have been navigating and resisting this landscape for years.
Surveillance itself is transnational: tools, playbooks, and data moves across borders as easily as money. And so we, too, continue our work, documenting abuses, sharing security knowledge, and collectively organizing against these violent systems.
This is the third installment of a blog series reflecting on the global digital legacy of the 2011 Arab uprisings. Read the rest of the series here.
Writer uses AI in New York Times book review and accidentally plagiarizes other review
Apr. 8th, 2026 07:23 amAlex Preston used AI in a book review for the New York Times and ended up lifting bits of a review from the Guardian. Emma Loffhagen reports for the Guardian:
Language that appears to be lifted from the Guardian review includes descriptions of characters – “lazy Machiavellian Stefano” appears as “lazy, Machiavellian Stefano” in the New York Times version – and the concluding assessment of the novel: the Guardian review states that the book is “most significantly a song of love to a country of contradictions, battered, war-torn, divided, misguided and miraculous: an Italy where life is costume and the performance of art, and where circuses spring up on wasteland”; while the New York Times version says the characters “populate what is ultimately a love song to a country of contradictions: battered, divided, misguided and miraculous. This is an Italy where life is performance, where circuses rise on wasteland.”
I’m pretty sure Preston is going to need a pseudonym soon.
Tags: Guardian, New York Times, plagiarism
(no subject)
Apr. 7th, 2026 07:12 pmOtherwise sun and snow do make a change from the chronic rain showers and also what was probably thundersnow last night. Whether it's the rain or whether it's a new stage of decrepitude, but my wrists are now catching and panging arthritically in the fashion of my April elbows. Last month I could skip acupuncture no problem, but having missed last week's session was clearly a bad idea. Have also ballooned with water weight as my ankles and scale inform me, alas. Time to drop the vodka coolers and reintroduce the 1.5 litres of water again.
Grammar
Apr. 7th, 2026 08:22 pmToday's xkcd:

Mouseover title: "Communication is one of the most popular ways to transmit information, ahead of rivals such as"
The explanation and discussion on explainxkcd.
Remembering Jim Quinn.
Apr. 7th, 2026 08:20 pmStephen Fried’s fond reminiscence of Jim Quinn (Philadelphia magazine, 10/19/2020) came out over five years ago, but I just discovered it, and since Quinn is one of my language heroes (first touted just a few weeks into the existence of LH, reinforced in 2004, 2007, and 2013) I wanted to share it with y’all. I’ll quote the language-related passages, but he led an interesting life in general, so I recommend the whole thing:
Jim Quinn was one of Philadelphia’s finest, funniest, and smartest writers — of longform journalism, essays about food and language, and poetry for the first four decades of his career, and later of fiction as well. He was also, arguably, the city’s longest-living, longest-haired, and most prolific link to the best things about the 1960s, maintaining throughout his 85 years a sense of wonder and humor, political commitment, righteous indignation, and shrugging indifference to authority. […]
Quinn could write the most gorgeous sentences. But much of the joy of his reportage was his amazing attention to details that told the story better than he could. “He describes everything, yes everything, in most specific terms since euphemism is a word he has never heard,” said the New York Times Book Review in 1972 of his first major book, Word of Mouth: A Completely New Kind of Guide to New York Restaurants. […]
In his late 20s, Quinn was convinced by friends to return to college. In 1963 he enrolled at Temple University, where he got involved in campus politics and anti-war protests. […] He was, at the time, working toward his PhD in English literature — writing a dissertation on the Scottish poet Hugh MacDiarmid, and lots of his own poetry. But editors who were fans of his food writing started reaching out with assignments. […]
That same year, Quinn published his second major book, American Tongue and Cheek: A Populist Guide to Our Language, in which he argued that English was becoming more and more democratized, and lampooned those trying to hold on to old formal usages. Critic Christopher Lehmann-Haupt in The New York Times Book Review called the book “outrageous and delightful.” While he found some parts infuriating, he noted “as Mr. Quinn writes, ‘If this book doesn’t make you angry, it wasn’t worth writing.’”
In an interview about the book with Terri Gross on “Fresh Air” — when the show was in its local infancy, complete with call-ins — he defended words like “hopefully” that were coming into common usage despite the horror of the grammar police. He was astonished how worked up people could get about new words being accepted by the print media. “You can confess to the most horrible kind of sexual practices,” he joked, “and people will say ‘well, we have to understand that sort of thing’ [to] … show their tolerance. But say the word ‘irregardless’ and say you have no intention of dropping it from your vocabulary and they become utterly infuriated!” He preached “new words are new tools.”
He and Gross also had a funny conversation about the Philadelphia accent, which she was just learning and he was unlearning. “I can’t say ‘att-y-tude’ any more,” he explained. “But I remember we used to say ‘grat-y-tude, what a lovely at-y-tude for a ‘prost-y-tute’ to have.” Gross burst out laughing.
Among the language police Quinn criticized was William Safire, who at the time was two years into his “On Language” column for the New York Times Magazine. He not only appreciated the book by Quinn — whom he referred to as “a poet and food columnist” — but soon after reviewing it Safire invited Quinn to write the “On Language” column when he was on vacation.
“The idea that he could jump the gap from writing for alternative weeklies to writing Safire’s column for the Times, and stand in for the nation’s grammarian — amazing,” recalled bestselling author Steven Levy, who worked with Quinn at the Drummer and Philadelphia. “Such a renaissance guy, and also the ultimate free agent, always moving publication to publication.” Quinn also later wrote a language column for The Nation.
I continue to recommend American Tongue and Cheek, and I’m delighted to learn he was a fan of Hugh MacDiarmid, one of my own poetic heroes (whom I also touted back in 2002). And if I ever knew he’d written the “On Language” column when Safire was on vacation, I’d forgotten.